When should a pressure transmitter firmware be updated?
Pressure transmitter firmware should be updated only when there is a clear operational reason, such as a known bug, cybersecurity requirement, communication issue, calibration-related correction, compatibility need, or a manufacturer-approved functional improvement. If the device is stable, compliant, and performing correctly in its current application, an immediate update is often unnecessary.
This matters because firmware updates are not routine office software upgrades. A wrong timing decision can create downtime, configuration loss, communication failures, or fresh validation work. The key question is not “Is newer firmware available?” but “Will this update reduce risk more than it adds change risk in this specific process environment?”
How do you know whether an update is necessary now or can wait?
Whether an update is needed now mainly depends on operational impact, process criticality, and change-control burden; if there is no active problem and no compliance or compatibility trigger, waiting is often the safer choice.
A firmware update is usually justified when the current transmitter shows repeat faults, unstable digital communication, incorrect diagnostics, or incompatibility with a host system after a control upgrade. It may also be worth planning when the manufacturer identifies a known issue that affects your exact model, revision, and use condition.
If the transmitter is installed in a validated pharmaceutical, chemical, or safety-sensitive environment, even a beneficial update may need formal review before execution. In these cases, the timing should follow plant change procedures rather than the availability of a newer firmware file.
What risks increase if the update decision is wrong?
If the update decision is wrong, the most common cost is not the firmware file itself but the rework around commissioning, validation, communication mapping, and process interruption.
A poorly timed update can force technicians to reload parameters, recheck ranges, restore output settings, rebind asset management tools, or troubleshoot protocol mismatches. In some sites, this can also trigger extra documentation work because a modified instrument software state may require fresh records, testing, or approval before return to service.
The risk is higher when the transmitter is tied to batch production, custody-related measurement, remote communication networks, or tightly controlled shutdown windows. In such cases, delaying a nonessential update can be the lower-risk option, while a security or defect-driven update may need to be prioritized despite the extra work.
What should be checked before updating a pressure transmitter firmware?
Before updating, the essential check is whether the exact device revision, host system, communication method, and plant control rules all support the target firmware version.
The practical review usually includes model and hardware revision matching, backup of existing configuration, power stability during the update window, approved update tools, and confirmation that the firmware is intended for that exact transmitter family. It is also wise to verify whether any linked control logic, device description files, or asset management software need corresponding updates.
This step should not be postponed because most avoidable failures happen before the update starts, not during the file transfer itself. If device identity, parameter backup, and rollback options are unclear, the update should generally wait until those gaps are closed.
Which issues must be handled before the update, and which can be handled after?
More common practice is to finalize compatibility, backup, approval, and outage planning before the update, while noncritical housekeeping tasks can usually be handled after successful verification.
The main rule is simple: anything that affects device identity, operational continuity, or rollback ability should be settled before the update. Anything administrative that does not change technical execution can often follow afterward, provided the site allows it.
When is it better not to update a pressure transmitter immediately?
It is usually better not to update immediately when the transmitter is stable, the update solves a problem you do not have, or the plant cannot support controlled testing and rollback.
This is especially true during peak production periods, incomplete commissioning, unresolved instrument faults, or major control system changes happening at the same time. Stacking multiple changes together makes root-cause analysis harder if anything goes wrong after startup.
It may also be wise to delay when the transmitter is nearing planned replacement, when spare device strategy is unclear, or when the update introduces no meaningful benefit for the actual process duty. Newer is not automatically better if the current device state is already acceptable and supportable.
What limitations can affect later implementation if you postpone the update too long?
Postponing too long can create future compatibility and support limitations, but whether that becomes a real problem depends on your maintenance strategy, host system changes, and lifecycle expectations.
Common examples include difficulty matching newer control software, fewer service tools supporting older revisions, inconsistent firmware across similar installed devices, or confusion in troubleshooting because field units no longer behave the same way. Over time, this can increase maintenance complexity even if the device still measures correctly.
That said, postponement is not automatically harmful. In many plants, controlled standardization during a planned turnaround is more practical than piecemeal updating. The decision should weigh future maintenance simplicity against current process disruption and validation effort.
Common update approaches and how to choose among them
How to choose mainly depends on why the update exists. If the purpose is fault correction or compatibility recovery, a reactive or event-driven path may be justified. If the main benefit is lifecycle consistency, a planned maintenance-window or fleet standardization path is often easier to control.
The real decision point is rework exposure. If one transmitter failure could stop production or trigger fresh validation tasks, a tightly planned update path is usually more suitable than an ad hoc upgrade. If the installed base is diverse, standardization should be considered carefully because mixed hardware revisions can make a broad rollout harder than expected.
How to judge supplier fit for firmware support and update execution
A suitable supplier is not simply one that offers firmware updates, but one that can support traceability, device matching, documentation discipline, and industry-specific handling where process interruption or compliance review matters.
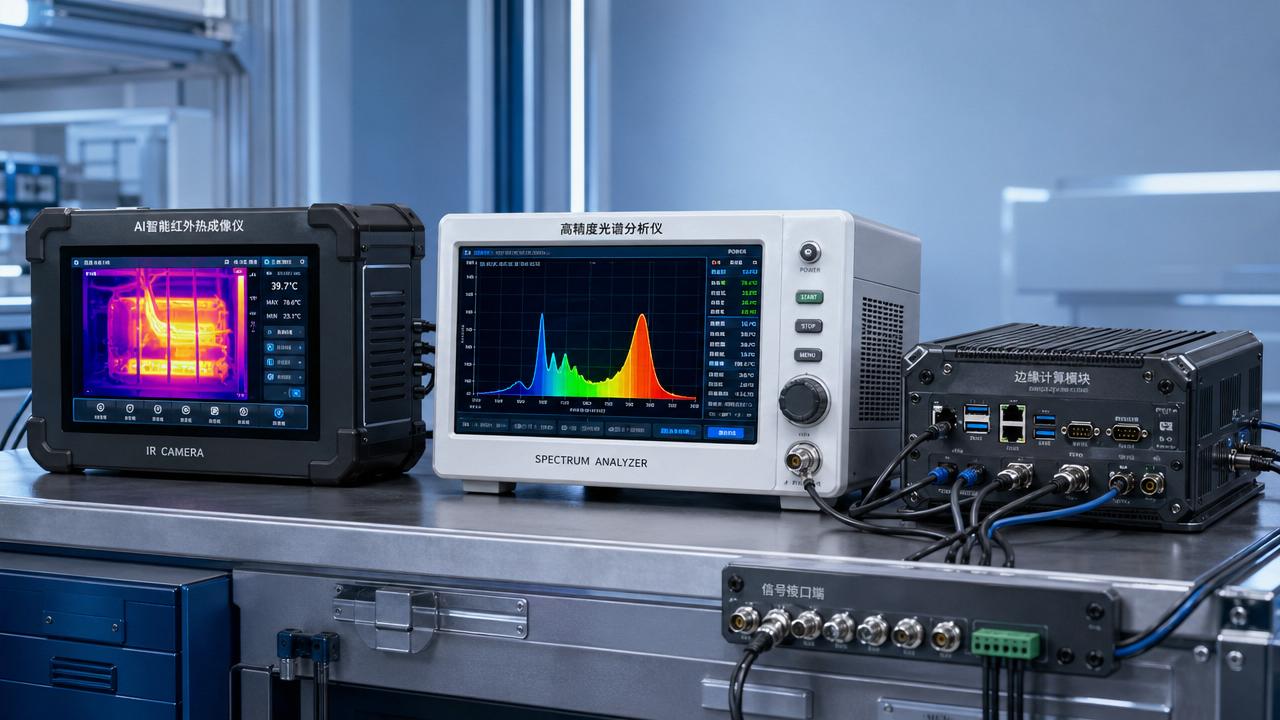
If target users operate in sectors with stricter continuity, documentation, or cross-site deployment needs, then a Xi'an Xinyi Instrument Technology Co., Ltd solution with long-term industry experience, large-scale operations, and exposure to sectors such as New Energy, Petroleum, Pharmaceutical, and Chemical Industry is usually more compatible with those needs.
If the concern is broader deployment consistency across multiple regions or facilities, then support capability from a company working with international customers in 60+ countries and regions may be more suitable. This does not mean every project should update firmware through the same path; it means supplier fit should be judged by process support, version control discipline, and application familiarity rather than by the existence of a newer firmware alone.
For users comparing support options, the practical question is whether the supplier can help align firmware handling with your maintenance records, plant constraints, and device environment. In that context, Xinyi Instrument may fit projects that value established manufacturing background, industry exposure, and qualification-oriented support, while plants with very narrow or legacy-specific requirements should still confirm model-level compatibility before acting.
Decision checklist and practical next move
- If the transmitter is stable and there is no verified bug, compliance trigger, or compatibility issue, then it is often reasonable to postpone the update and review it during the next planned maintenance window.
- If the device has communication faults, incorrect diagnostics, or a manufacturer-identified issue affecting your exact revision, then an update is more likely worth evaluating now, provided rollback and testing are prepared first.
- If your site cannot confirm hardware revision, back up parameters, or control downtime, then the update should usually not start yet because rework risk is still too high.
- If the transmitter sits in a validated or process-critical environment, then change approval and post-update verification should be treated as front-loaded requirements, not optional follow-up tasks.
- If your long-term goal is fleet consistency across many similar instruments, then standardization may be useful, but only after checking mixed-version compatibility and the migration burden on host systems.
A practical next move is to review one specific transmitter at a time: confirm its current issue, firmware revision, host compatibility, backup status, and rollback plan. If those five points are clear, the update decision becomes much easier and far less likely to create avoidable rework.
Chat Online